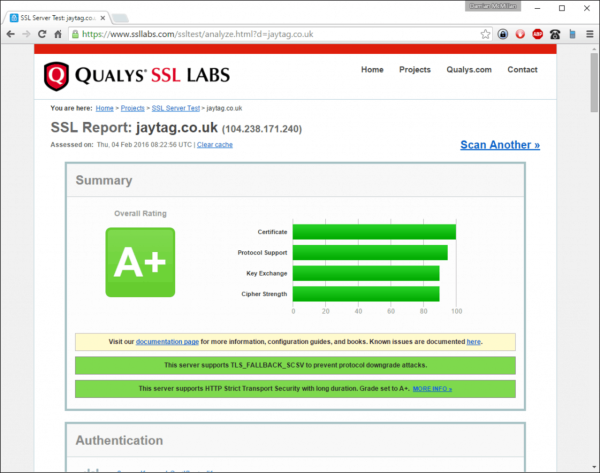
We've recently been testing sites with the Qualys SSL Server Test here: https://www.ssllabs.com/ssltest/index.html
By default, the SSL settings on Vesta are good - but it's not possible to get an A+ rating without making some changes to the nginx configuration files.
Although SSL Labs do give an indication as to where the SSL rating is low, it's not very easy to see exactly what needs to be changed with nginx to get the A+ rating. The key things to improve:
- Limit the SSL ciphers that can be used
- Add HTTP Strict Transport Security with long duration
- Enable SSL stapling
Firstly, you have to SSH onto your vesta server, and edit the main nginx conf file:
nano /etc/nginx/nginx.conf
Then, add the following settings:
# Improved SSL settings – as suggested by jaytag.co.uk
ssl_session_cache builtin:1000 shared:SSL:10m;
add_header Strict-Transport-Security "max-age=63072000; includeSubDomains; preload";
add_header X-Frame-Options DENY;
ssl_stapling on; # Requires nginx >= 1.3.7
ssl_stapling_verify on; # Requires nginx => 1.3.7
resolver 8.8.4.4 8.8.8.8 valid=300s;
resolver_timeout 5s;Then save the file.
One of the warnings you will receive is "This server supports weak Diffie-Hellman (DH) key exchange parameters" so you have to generate strong DH key parameters. There is some interesting info here about the duration of calculating the primes: http://security.stackexchange.com/questions/95178/diffie-hellman-parameters-still-calculating-after-24-hours so taking their advice, we will use the -dsaparam switch to speed up the process.
mkdir /etc/pki/nginx
openssl dhparam -dsaparam -out /etc/pki/nginx/dhparam.pem 4096If you are feeling super secure (takes a few hours to randomly generate the primes) do this instead:
openssl dhparam -out /etc/pki/nginx/dhparam.pem 4096
When complete, you can then edit the nginx parameters:
cp /home/jaytag/conf/web/snginx.conf /home/jaytag/conf/web/snginx.conf.old
nano /home/jaytag/conf/web/snginx.confAdd in the top section after the line ssl on:
ssl_stapling on;
ssl_dhparam /etc/pki/nginx/dhparam.pem;
ssl_session_timeout 24h;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_ciphers kEECDH+AES128:kEECDH:kEDH:-3DES:kRSA+AES128:kEDH+3DES:DES-CBC3-SHA:!RC4:!aNULL:!eNULL:!MD5:!EXPORT:!LOW:!SEED:!CAMELLIA:!IDEA:!PSK:!SRP:!SSLv2;
ssl_prefer_server_ciphers on;
add_header Strict-Transport-Security "max-age=31536000;";
add_header Content-Security-Policy-Report-Only "default-src https:; script-src https: 'unsafe-eval' 'unsafe-inline'; style-src https: 'unsafe-inline'; img-src https: data:; font-src https: data:; report-uri /csp-report";Then save the file.
The last step is to restart nginx:
service nginx restart
Now re-test on SSL Labs. Success!